T1158: Hidden files before T1504: Powershell profile |
||
|---|---|---|
| .github | ||
| deployment_scripts | ||
| docker | ||
| envs | ||
| monkey | ||
| .gitignore | ||
| .gitmodules | ||
| .travis.yml | ||
| CONTRIBUTING.md | ||
| LICENSE | ||
| README.md | ||
README.md
Infection Monkey
Data center Security Testing Tool
Welcome to the Infection Monkey!
The Infection Monkey is an open source security tool for testing a data center's resiliency to perimeter breaches and internal server infection. The Monkey uses various methods to self propagate across a data center and reports success to a centralized Monkey Island server.
The Infection Monkey is comprised of two parts:
- Monkey - A tool which infects other machines and propagates to them.
- Monkey Island - A dedicated server to control and visualize the Infection Monkey's progress inside the data center.
To read more about the Monkey, visit infectionmonkey.com.
Screenshots
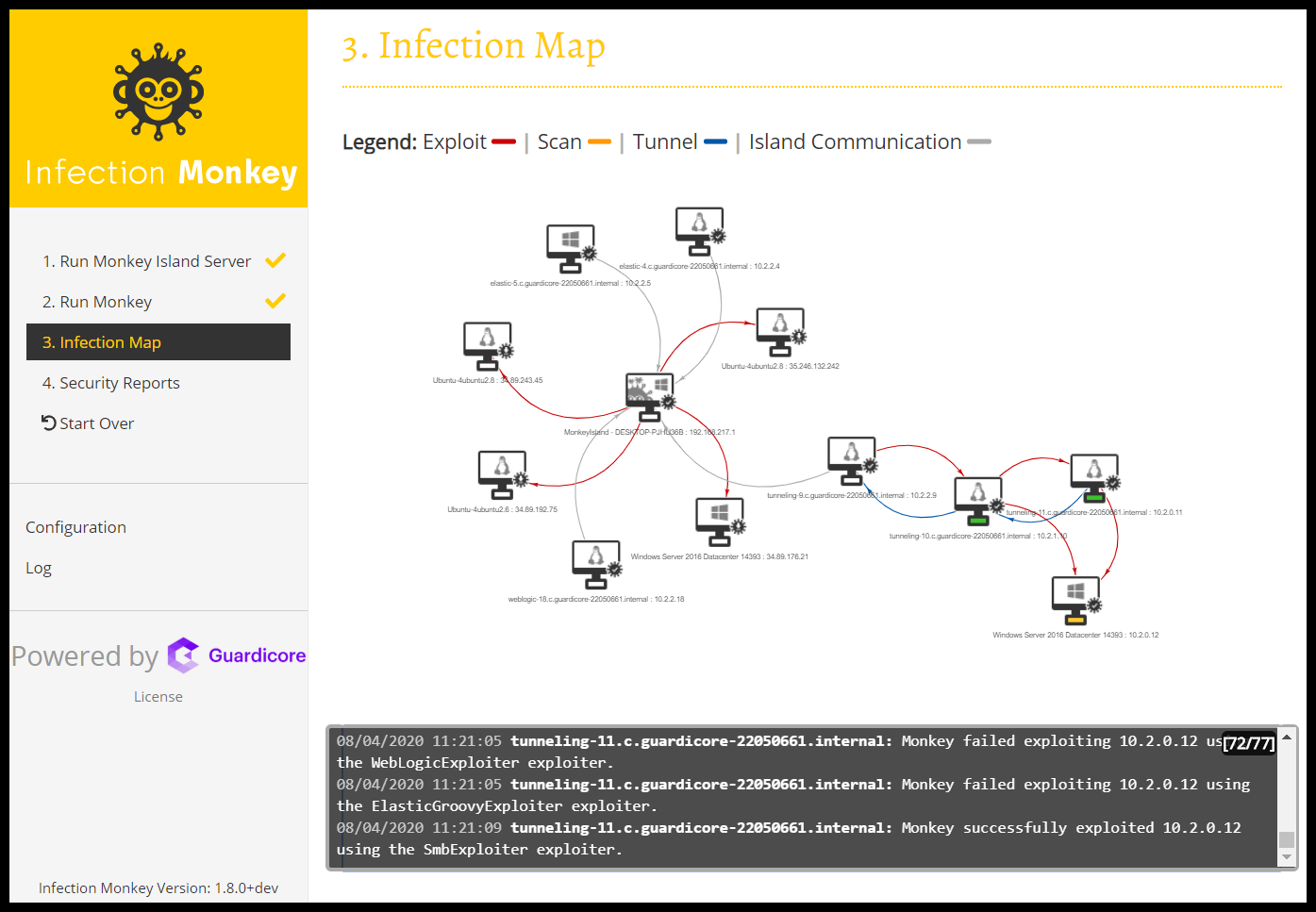
Map
Security report

Zero trust report

ATT&CK report

Main Features
The Infection Monkey uses the following techniques and exploits to propagate to other machines.
- Multiple propagation techniques:
- Predefined passwords
- Common logical exploits
- Password stealing using Mimikatz
- Multiple exploit methods:
- SSH
- SMB
- WMI
- Shellshock
- Conficker
- SambaCry
- Elastic Search (CVE-2015-1427)
- Weblogic server
- and more
Setup
Check out the Setup page in the Wiki or a quick getting started guide.
The Infection Monkey supports a variety of platforms, documented in the wiki.
Building the Monkey from source
To deploy development version of monkey you should refer to readme in the deployment scripts folder. If you only want to build the monkey from source, see Setup and follow the instructions at the readme files under infection_monkey and monkey_island.
Build status
| Branch | Status |
|---|---|
| Develop | |
| Master |
Tests
Unit Tests
In order to run all of the Unit Tests, run the command python -m pytest in the monkey directory.
To get a coverage report, first make sure the coverage package is installed using pip install coverage. Run the command
coverage run -m unittest in the monkey directory and then coverage html. The coverage report can be found in
htmlcov.index.
Blackbox tests
In order to run the Blackbox tests, refer to envs/monkey_zoo/blackbox/README.md.
License
Copyright (c) Guardicore Ltd
See the LICENSE file for license rights and limitations (GPLv3).


